Cybersecurity Capability Maturity Self-Assessment
Disclaimers
All contents Copyright Purdue University. All rights reserved. This is an official World Wide Web page of Purdue University. Additional information can be found at the University Copyright Office. This site complies with the Purdue University’s Privacy Policy regarding data that you supply.
This report and the tool used to produce it provide neither evidence of compliance with any regulation or standard, nor legal advice. The analysis and provided in this document are based on the responses you provided when completing this survey and the recommendations are generalized based on the limited information requested in the survey. By using these tools and reports, you acknowledge these conditions and limitations. To obtain a thorough analysis of the maturity of your organization’s cybersecurity posture, please contact George Bailey, Assistant Director for Security Services - baileyga@purdue.edu.
Assessment Structure and Maturity Scoring
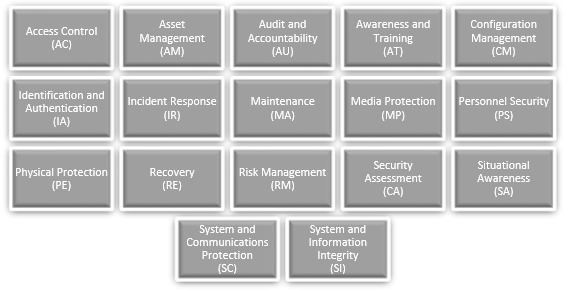
This assessment uses the structure, categorization, questions, and associated maturity levels described in the “Cybersecurity Maturity Model Certification” document published by the United States Office of the Undersecretary of Defense for Acquisition & Sustainment (OUSD(A&S)) v. January 2020.
To produce a consistent scoring mechanism in support of the report that results from the following self-assessment, cyberTAP has assigned three potential answer choices for each assessment question: Satisfied, Partially Satisfied, and Not Satisfied. If your organization has implemented controls that completely fulfill the control requirements related to the question, you should answer “Satisfied” to the question. If your organization’s information security controls meet part of the requirement discussed in the question, you should answer “Partially Satisfied”. If no controls exist within your organization that address the risks/controls discussed in the question, you should respond with “Not Satisfied”. Each response is assigned a point value. The values assigned to your responses to each question are totaled and reported to you both as a maturity score by control category (as categorized in the OUSD(A&S) document), and as an overall maturity score. In summary, the assessment content is replicated from the OUSD(A&S) document, but the assignment of points to responses, totaling of points, assignment of maturity level to point totals, and representations of maturity levels to you and your organization is the prerogative of cyberTAP and not an official determination of the OUSD(A&S) or United States Department of Defense. This self-assessment is just a guide. Finally, the OUSD(A&S) currently assigns the following descriptions of cybersecurity processes and institutionalization to each corresponding maturity level.
| Maturity Level | Maturity Level Description | Processes |
|---|---|---|
| ML 1 | Performed |
There are no maturity processes assessed at Maturity Level 1. An organization performs Level 1 practices but does not have process institutionalization requirements. |
| ML 2 | Documented |
Establish a policy that includes [DOMAIN NAME]. Document the CMMC practices to implement the [DOMAIN NAME] policy. |
| ML 3 | Managed | Establish, maintain, and resource a plan that includes [DOMAIN NAME]. |
| ML 4 | Reviewed | Review and measure [DOMAIN NAME] activities for effectiveness. |
| ML 5 | Optimizing | Standardize and optimize a documented approach for [DOMAIN NAME[ across all applicable organization units. |



